 Hello everyone, Zimbra Collaboration includes anti-SPAM and antivirus technologies such as Postscreen, Spamassasin, Amavis, ClamAV, etc. But sometimes, for legal reasons, etc., we need to block certain senders or even entire domains from sending unsolicited email.
Hello everyone, Zimbra Collaboration includes anti-SPAM and antivirus technologies such as Postscreen, Spamassasin, Amavis, ClamAV, etc. But sometimes, for legal reasons, etc., we need to block certain senders or even entire domains from sending unsolicited email.
To do this, we will use the tools that come native to Zimbra Collaboration, and with a few simple commands, we can granularly protect our email users. Here’s how…
Create a file called /opt/zimbra/common/conf/postfix_reject_sender with the list of email addresses and domains to be rejected in the below format:
user@domain.com REJECT domainX.com REJECT
As Zimbra user, execute the zimbraMtaSmtpdSenderRestrictions command:
zmprov ms 'yourzimbraservername' +zimbraMtaSmtpdSenderRestrictions "check_sender_access lmdb:/opt/zimbra/common/conf/postfix_reject_sender"
Then we will need to postmap it:
/opt/zimbra/common/sbin/postmap /opt/zimbra/common/conf/postfix_reject_sender
We can wait around 60 seconds until the Zimbra MTA pick up the changes, or force the changes with a restart to the MTA services with:
zmmtactl restart
You will see an output similar to this:
Rewriting configuration files...done. Stopping saslauthd...done. Starting saslauthd...done. /postfix-script: refreshing the Postfix mail system
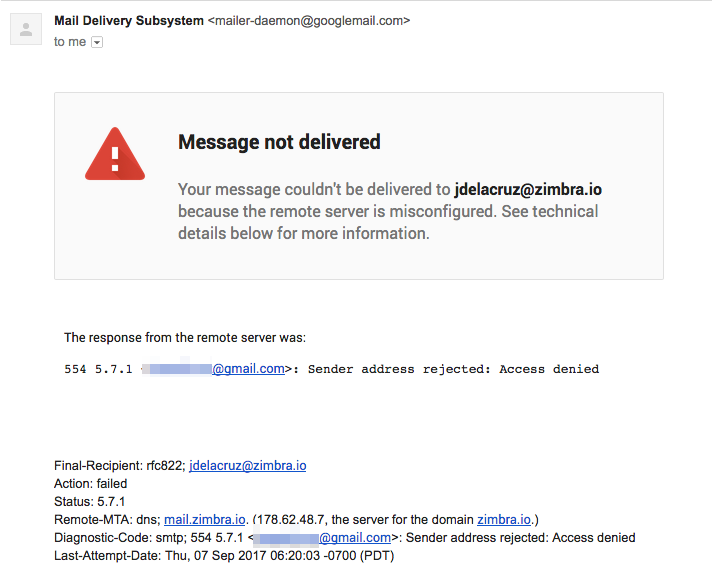
If one of the blocked users or domains tries to send us an email, on the zimbra.log you will see something similar to this, (mind the error saying “Sender address rejected: Access denied”):
Sep 7 14:19:57 mail postfix/postscreen[13755]: CONNECT from [74.125.82.45]:32831 to [178.62.48.7]:25 Sep 7 14:20:01 mail zimbramon[15143]: 15143:info: 2017-09-07 14:20:01, QUEUE: 0 0 Sep 7 14:20:03 mail postfix/postscreen[13755]: PASS NEW [74.125.82.45]:32831 Sep 7 14:20:03 mail postfix/smtpd[13756]: connect from mail-wm0-f45.google.com[74.125.82.45] Sep 7 14:20:03 mail postfix/smtpd[13756]: Anonymous TLS connection established from mail-wm0-f45.google.com[74.125.82.45]: TLSv1.2 with cipher ECDHE-RSA-AES128-GCM-SHA256 (128/128 bits) Sep 7 14:20:03 mail postfix/smtpd[13756]: NOQUEUE: filter: RCPT from mail-wm0-f45.google.com[74.125.82.45]: <user1@gmail.com>: Sender address triggers FILTER smtp-amavis:[127.0.0.1]:10026; from=<user1@gmail.com> to=<jdelacruz@zimbra.io> proto=ESMTP helo=<mail-wm0-f45.google.com> Sep 7 14:20:03 mail postfix/smtpd[13756]: NOQUEUE: reject: RCPT from mail-wm0-f45.google.com[74.125.82.45]: 554 5.7.1 <user1@gmail.com>: Sender address rejected: Access denied; from=<user1@gmail.com> to=<jdelacruz@zimbra.io> proto=ESMTP helo=<mail-wm0-f45.google.com> Sep 7 14:20:03 mail postfix/smtpd[13756]: disconnect from mail-wm0-f45.google.com[74.125.82.45] ehlo=2 starttls=1 mail=1 rcpt=0/1 data=0/1 quit=1 commands=5/7
The blocked sender will see the next error:
 And that’s it for today’s How-To. In future blog entries, we’ll show you how to blacklist and whitelist IPs, or a range of IPs.
And that’s it for today’s How-To. In future blog entries, we’ll show you how to blacklist and whitelist IPs, or a range of IPs.
Additional Links
- See how to block incoming users or domains for older Zimbra versions – https://wiki.zimbra.com/wiki/Domain_level_blocking_of_users
- Download Zimbra Collaboration Open Source – https://www.zimbra.com/try/zimbra-collaboration-open-source/
- Download Zimbra Collaboration Network Edition – https://www.zimbra.com/try/zimbra-collaboration-network-edition/

Great. I was posted alternative to block incoming users or domains using bahasa :)
https://www.ilmuzimbra.com/tips-blacklists-dan-whitelists-zimbra
Hello,
Is this working for blocking outgoing emails also, to certain domains or users?
I want to block some internal users from sending email to certain domains or email addreses. Is this possible with Zimbra?
Thank you!
Hi Alex,
It’s possible. You can follow this tutor http://wiki.zimbra.com/wiki/Restrict_users_to_certain_domain
i have done with same command on zimbra 8.6 open source edition, but my zimbra stop working, no send no receive from any domain.
Hello Arlsam,
For 8.6 is different, and the steps are on the wiki, you can remove it from the next document:
And remove the next line
Then restart the services
Configuration dont save parameter (Release 8.7.5_GA_1764.RHEL6_64_20170314032533 RHEL6_64 FOSS edition.):
[zimbra@zimbra ~]$ zmprov ms zimbra.******.com.br +zimbraMtaSmtpdSenderRestrictions “check_sender_access lmdb:/opt/zimbra/postfix/conf/postfix_reject_sender”
[zimbra@zimbra ~]$ zmmtactl restart
Rewriting configuration files…done.
Stopping saslauthd…done.
Starting saslauthd…done.
/postfix-script: refreshing the Postfix mail system
[zimbra@zimbra ~]$ postconf | grep postfix_reject_sender
[zimbra@zimbra ~]$
Hi Fernando, Guys,
i have exactly the same issue on 8.8.8_GA_2009.UBUNTU16_64.20180322150747 Ubuntu Server 16.04.4
i have this in /opt/zimbra/conf/zmconfigd/smtpd_sender_restrictions.cf:
%%contains VAR:zimbraMtaSmtpdSenderRestrictions check_sender_access lmdb:/opt/zimbra/conf/postfix_reject_sender%%
but it is not added in main.cf
Fernando did you succeeded to permanently add the postfix_reject_sender to main.cf?
Hello Everybody,
There is also a Zimlet that allows users to block/allow senders and domains, that is based on the amavis in Zimbra, its over here:
https://zimbra.org/extend/items/view/whitelist-blacklist-sender
zimbra can see all log event all user send out or comming mail content on log file ?
Hi,
Is it still possible with Zimbra 8.7 to specify wildcard entries, like say “*.badsender.com”? Thanks for the help!
LG
@Luigi, I would say yes! Since this blog post is only 2 months old.
And it can be done with whitelist-blacklist-sender for sure!
Dear Jorge,
If we implemented reject_authenticated_sender_login_mismatch and then we can add “check_sender_access lmdb:/opt/zimbra/common/conf/postfix_reject_sender” because attribute ‘zimbraMtaSmtpdSenderRestrictions’ cannot have multiple values. Is it right?
Regards,
Minh